Most fleets will be using devices that come with a monthly service plan, most often associated with a connection to the cellular data network. By definition, the connectivity of ELDs make them an Internet of Things (IoT) device. This may cause some concerns over cybersecurity.
In 2016, AT&T reported a 3,198 percent increase over the last three years in the number of attackers scanning for vulnerabilities in IoT devices. AT&T also conducted a survey last year of businesses to gauge their potential security threats. Fifty-eight percent said they were not confident in the security of their IoT devices.
Cybersecurity was hardly a concern 25 years ago when fleets began using mobile communications systems to connect with drivers and vehicles via satellite networks. With millions of ELD devices about to go online, could they be the gateway for hackers to gain access to sensitive information?
Probably not, but here are four possible areas of concern:
1. Remote control trucks
The University of Michigan made news in 2016 when researchers presented at an August conference results from their experiments with the vulnerability of big rigs’ electronic systems. Researchers plugged into a 2006 tractor’s diagnostics port, and this was in part the result:
By sending digital signals within the internal network of a big rig truck, the researchers were able to do everything from change the readout of the truck’s instrument panel, trigger unintended acceleration, or to even disable one form of the semi-trailer’s brakes.
Since the late 1990s, fleets have used telematics devices to remotely plug into the controller area network (CAN) of trucks to capture data from their engines and electrical-mechanical systems.
 Fleet Complete, Geotab and BigRoad are among the dozens of mobile-device-based options for ELD compliance.
Fleet Complete, Geotab and BigRoad are among the dozens of mobile-device-based options for ELD compliance.Incidents of remotely hacking into the ECMs of engine and braking systems have not happened — yet.
Spokespeople from ELD suppliers say the probability of hacking into electronic logs — either the current AOBRD (395.15) and the new ELD standard (395.16) — to access the CAN bus of vehicles is virtually impossible. That’s because ELDs are provisioned to read data only.
“We don’t give (our application) rights to be able to write or make requests. All we do is read,” says Marco Encinas, a marketing and product manager of Global Platforms at Teletrac Navman, which offers the Director ELD product. “There is no protocol in the system that allows us to engage, change code, or manipulate the ECM computer on the vehicle.”
As an extra layer of precaution, PeopleNet, one of the two largest fleet mobility providers, has embedded chips in its ELD devices in order to authenticate the connection between the device in the vehicle and its cloud management system.
“Our latest devices will all ship with an encryption chip built in to authenticate the device to the cloud in addition to standard authentication of the driver’s credentials upon login,” says Eric Witty, vice president of product. “That way we have assurance that both the device and the person are authenticated in our system.”
And through PeopleNet’s partnerships with truck OEMs, “we continue to undergo security audits and improvements to our software and hardware solutions to ensure we minimize any risk of these telemetry devices being exploited to access the vehicle,” he adds.
2. Access to ELD data
Besides preventing ELDs from talking to vehicles, the suppliers interviewed for this article say their applications are restricted from sharing data with other applications on the device or vehicle.
 Teletrac’s Director ELD device runs on tablets with Garmin navigation.
Teletrac’s Director ELD device runs on tablets with Garmin navigation.“We follow secure code development practices that isolate the ELD application code from other applications on the devices,” says Andrew Dondlinger, Navistar’s vice president for Connected Services. “The ELD application also requires positive user credentials before allowing for the collection of the vehicle’s ELD data by any user, or by any other application.”
Navistar offers an ELD app that connects the driver’s mobile device to the OnCommand Connection Telematics device. The app is available through its new OnCommand Connection Marketplace.
PeopleNet has traditionally favored using company-owned, personally enabled (COPE) communications devices as part of its strategy to allow fleets to deploy proprietary company apps and approved third-party programs on the same device that runs their PeopleNet software, Witty says.
PeopleNet envisions having “companion apps” that will give drivers access their own log data as well as giving access through a secure driver portal.
“The security concerns are much the same as the ELD device itself. We will address them by ensuring we are using the same standards such as secure HTTP (SSL/TLS) similar to how banks secure communication for their mobile applications,” he says.
Teletrac provides a Garmin GPS tablet to run its ELD application. The only other app on the device is Garmin navigation. “We don’t allow third-party apps to be downloaded,” Encinas says. The tablets communicate through serial connection to a black box that has cellular connectivity.
The display tablets do not have their own cellular connection, which prevents software from being loaded onto the devices.
“For us it’s about being able to control the types of data communicated to the hardware and to us to limit possibilities for distraction,” he says.
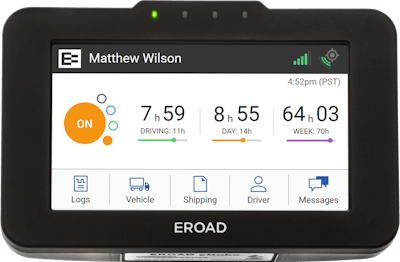
3. Reporting malfunctions
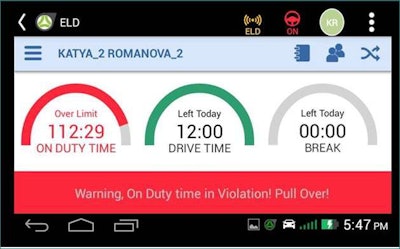
No ELD product on the market is foolproof. In the event of a hardware, software or connection malfunction the FMCSA requires that ELDs report the error to the driver and fleet management for support activities.

Similarly, if a malfunction is detected by Teletrac’s Director ELD application, the device continues to record any data that it can from the vehicle and the driver’s duty status. The driver is alerted by a fault message indicator and fleet management is alerted through the web portal to notify dispatchers.
Teletrac’s support team can do an over-the-air reset if needed, Encinas says.
4. Data privacy
Data privacy is another topic that surrounds industry-wide adoption of ELDs. Independent owner-operators may not want the carriers or freight brokers they work for to have visibility of their logbook data. On the other hand, fleets want visibility to identify drivers who have time remaining on their clocks to make an extra pickup or delivery, for example.
“The whole question about data gets typically framed in data privacy or data security. As a consumer you don’t want anybody to know where you’ve been, but in a business context, the area of privacy is much less prevalent,” says Dirk Schlimm executive vice president of Geotab, a telematics and ELD provider.
Some ELD providers see an opportunity to aggregate the hours-of-service and telematics data they collect from their customers. With their customers’ permission, they could use the data to power a freight matching system or a usage-based model for vehicle and liability insurance, for example.
“It will be very hard in the future for any business of any size to compete without data,” Schlimm adds. “You just have to give everybody secure and safe access to that data.”