
Two carriers were reported for theft in Southern California in the back half of 2022. At the beginning of August this year, another carrier came on the scene that could potentially be connected to those two carriers, but digital freight network Convoy gave the carrier a chance to prove itself, ultimately eliminating the carrier from the company’s network.
Convoy used its newly released real-time fraud detection system to give this carrier the boot.
“Generally, whenever we see risk for a carrier, we still give them the opportunity to prove their legitimacy. Sometimes, even good carriers may have something that looks wrong about them. We want to make sure that they can provide documentation – things like truck photos – to show that they are actually a good actor,” said Eric Libby, head of performance, compliance and trust at Convoy. “Carrier D was reported in the past week to have stolen at least eight shipments that we're aware of right now.”
But Convoy and its customers were not affected because of its new system, which confirmed the fraudulent nature of the carrier based on a digitally altered photo of a truck that a previous fraudulent carrier had used. And this information has been fed back into the Convoy system to make its model smarter over time.
The new system, which runs 24/7, constantly vetting carriers for changes, combines machine learning technology, forensic behavioral data, automation and industry collaboration to monitor risk in real-time, proactively block fraud before it can occur and more quickly apprehend perpetrators. It has resulted in a 90% reduction of cargo theft, double brokering and other forms of fraud in the Convoy network.
[RELATED: Technology drives major increase in double-brokering scams]
Cargo theft has been on the rise in recent years and continues to grow with each quarter. Cargo theft was up 57% year over year in the second quarter of 2023. A total of $223 million worth of cargo was lost in 2022. Trailer theft was up 17% year over year in the second quarter, and double brokering was up a whopping 400% year over year in the fourth quarter of 2022, according to data from CargoNet.
Seeing the rise in those statistics in the attempts of bad actors to join its own network, Libby said Convoy realized the need to fix these issues using its own data, giving the company ownership over its destiny and allowing it to react faster than it could if it purchased a solution from an outside vendor.
A different approach
Libby said some traditional vetting solutions, which rely primarily on manual process and human analysis that impedes scale, have gaps in their systems that let bad actors slip in, and a big part of that is an over-reliance on onboarding.
“A lot of traditional solutions will onboard a carrier once and then basically let that carrier do whatever happens after that point, and not continue to go back and make sure that that carrier is vetted over time,” he said.
Risk at onboarding is a single static data point, while a carrier’s risk profile and behavior can change over time, which is why Convoy’s system is “always on.” So rather than just looking at onboarding or looking at the point of booking a carrier on a shipment, Libby said Convoy is constantly looking for changes in a carrier’s risk profile from all interactions Convoy has with them to understand if they’re behaving differently – if there has been an increase in risk.
Other issues with traditional solutions include lack of information about individual drivers, which can be critical in mitigating and preventing fictitious pickups (up 600% in 2022); impartial assessments that can result in false positives that stifle the growth of legitimate carriers by blocking them from working with established brokerages; and failure to identify fraud networks.
That last one is what Convoy calls the whack-a-mole problem. Just because you eliminate one carrier from your system for fraudulent risk doesn’t mean you’re safe; they are often part of a larger fraud ring, and these entities keep popping back up, said Ryan Gist, associate general counsel at Convoy.
“This is sort of like swinging a sledge hammer trying to hit an ant in the dark – swinging over and over and over again,” Gist said. “Maybe they get some, but it’s not a very effective solution.”
Convoy’s solution
Gist said Convoy is leveraging some techniques that haven't been used in freight yet, borrowed from the financial industry, which has been dealing with fraud in significance, complexity and sophistication for 20-plus years.
At the core of Convoy’s real-time fraud detection system is machine learning technology that continually verifies the trustworthiness of carriers and identifies relationships between carriers. The company has been testing this system over the last six months with Fortune 1000 shippers and industry partners to address the shortcomings of traditional solutions.
As part of the onboarding process, carriers are put through a proprietary risk assessment model after they’ve satisfied mandatory insurance, operating authority and FMCSA carrier contact verification. Using publicly available and proprietary data, Convoy’s clustering model identifies latent connections between carriers and their personnel and then makes recommendations based on the risk level of those links.
Carriers flagged as high risk are immediately blocked from bidding on loads within the Convoy app. Those flagged with potential risk – like Carrier D previously mentioned – are asked to submit additional information to prove their legitimacy. Then all carriers flagged with any level of risk are reviewed by a member of Convoy’s trust and security team to make the final decision on network membership.
Network graphing, as Convoy calls it, is one of the most important elements in the system, Libby said.
“Rather than looking at all entities independently, we attempt and have found it successful to find connections between carriers – carriers that share similar information, how they access Convoy, what they access with and their behavior,” he said. “So … once we exit them, they're done; we can make sure that we can very easily understand if they try to come back into our network because we've seen that type of activity and block that at the source.”
Of course, a carrier’s risk profile can change over time. That’s why Convoy’s system continues to vet carriers after their initial onboarding – multiple times per day. Convoy looks at carriers for economic changes, sales of companies or onboarding of poorly vetted drivers, among other factors, to determine risk throughout its relationship with a carrier.
“We've seen that a bad actor can put on their best suit when they're onboarding and make it look like they're legitimate, but then the second they get into a network, they put the guard down, and then you start to catch other things that they're doing that link them to some other bad actors,” Libby said. “We're not trying to make a decision using one data point; we're trying to make a decision using a million data points along the way.”
Those data points include driver information as well. Convoy has built a multi-layered driver verification process to validate the accuracy of provided identification with the capability to provide the validated assigned driver directly to facilities to verify before releasing a shipment. The company is also looking for behavior identified with double brokering. As carriers book shipments, the system evaluates their schedules for practicality, and if deemed infeasible or high risk, loads are automatically removed from the carrier.
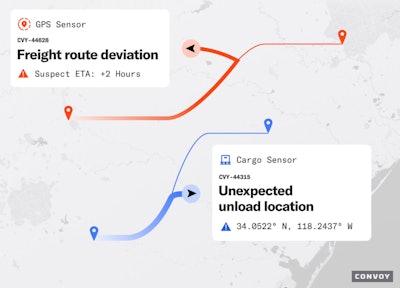
Once a load has been assigned to a carrier, Convoy’s system tracks every step of the shipment lifecycle, looking for anomalies and proactively alerting the team to any suspicious activity. GPS tracking enables the company’s systems to automatically determine if a shipment isn’t progressing to its destination as expected, and cargo sensors automatically send alerts if a shipment is being unloaded in an unexpected location.
[RELATED: Use of cargo cameras is on the rise]
But Libby said fraud doesn’t typically progress to the point of needing these processes as much because of the system’s preventative measures.
Gist said the industry sees fraud as something that just has to be dealt with when it happens.
“One thing that distinguishes this approach significantly is we hear from a lot of folks in the industry that fraud and theft are here to stay, and we just have to mitigate the best we can,” Gist said. “I think we fundamentally disagree with that. We’re talking 99.99%. Our goal is stopping it before it comes into our network.”























![Img 9401[87]](https://img.ccjdigital.com/mindful/rr/workspaces/default/uploads/2026/05/img-940187.vJq7SVGjUK.jpg?auto=format%2Ccompress&fit=crop&h=167&q=70&w=250)
